
Insiq Recovery Services
© 2024 Insiq Recovery Services
News & Insights
Explore account recovery, cyber safety, platform security, and incident response guidance from Insiq Recovery Services.

Updated March 30, 2026
How to Secure Your Facebook Account
Secure the control plane that protects Facebook: inbox, 2FA, sessions, and integrations. A containment-first playbook to prevent persistence and business asset loss.
Updated March 30, 2026
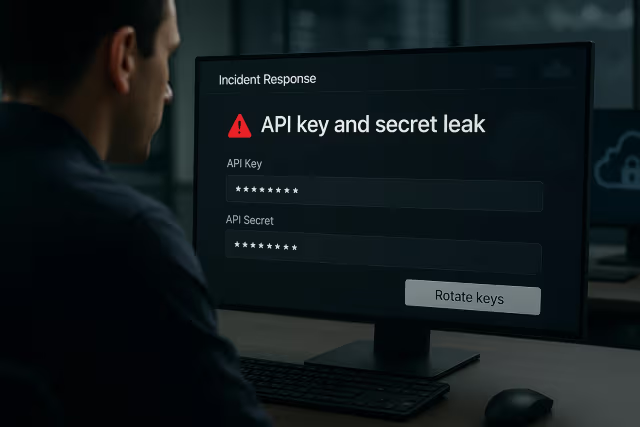
API Key and Secrets Leak Response: Contain, Rotate, and Map Blast Radius
When credentials are exposed, the difference between a contained incident and organizational catastrophe depends on immediate response velocity and exposure mapping.

Updated March 30, 2026
If Security Cameras Are Hacked: Containment, Privacy Risk, and Durable Fixes
IoT and surveillance infrastructure compromises require immediate isolation, firmware analysis, and network segmentation to prevent lateral movement and persistent surveillance.

Updated March 30, 2026
Can You Trust YouTube Kids? Risks and How to Use It Safely
Algorithmic content curation, data collection practices, and the false promise of filtered environments—understanding the real risks behind child-focused video platforms.

Updated March 30, 2026
Cybersecurity Lessons from High-Profile Incidents: How to Reduce Real-World Risk
Analyzing FireEye, SolarWinds, and CNA breaches reveals that detection/response capabilities and third-party risk management matter more than prevention perfection.

Updated March 30, 2026
When Advanced Tools Leak: Why Patching, Boundaries, and Recovery Still Decide Outcomes
State-sponsored tool leaks create commodity attack waves—operational discipline in exposure management and backup validation determines organizational resilience.

Updated March 30, 2026
If Sensitive Photos Were Leaked: Containment, Takedown, and Account Security
Non-consensual image distribution requires immediate damage control, platform reporting, and comprehensive digital security lockdown to prevent secondary victimization.

Updated March 30, 2026
When a Security Firm Is Breached: What the FireEye Incident Teaches
The December 2020 compromise of FireEye's red team tools demonstrates that no organization is immune and supply chain attacks threaten everyone.

Updated March 30, 2026
Conflict-Driven Cyber Headlines to Personal Safety: Protect Yourself from Impersonation and Phishing
Geopolitical tensions create exploitable emotional contexts—sophisticated phishing campaigns leverage conflict anxiety and urgency to compromise targets through false authority.

Updated March 30, 2026
Ransomware Groups and PR: What to Ignore and What to Fix
Criminal organizations now employ professional media strategies, 'charm offensives,' and direct journalist engagement to shape narratives and pressure victims.

Updated March 30, 2026
Yango Data Transfer Concerns: How to Reduce Location and Identity Exposure
Ride-sharing applications collect extensive location data, travel patterns, and personal information—creating high-value intelligence targets requiring privacy-first operational security practices.

Updated March 30, 2026
CNA Cyber Incident Lessons: Reduce Ransomware Leverage with Identity and Recoverability
Critical infrastructure protection requires Zero Trust architecture, immutable backups, and rapid incident response to deny ransomware operators their leverage.